NOTE: An update was added to this story at 4 p.m. ET, Aug. 20.
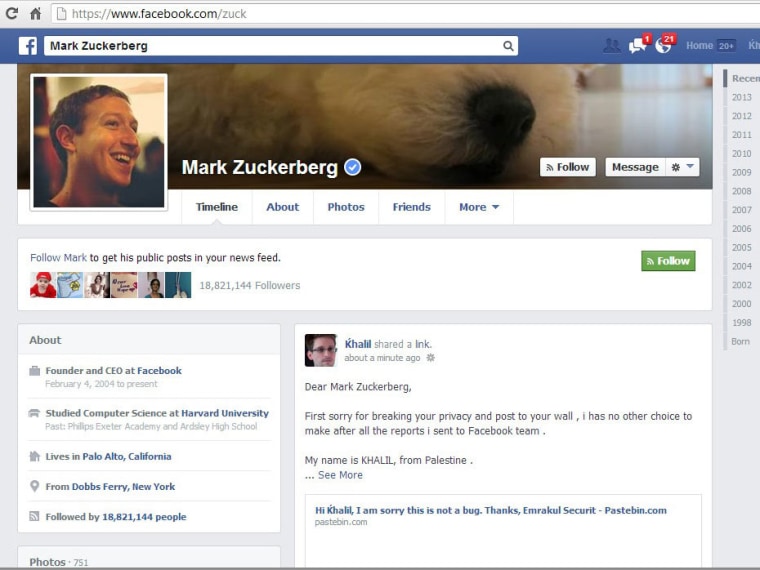
A security researcher attempting to report a site vulnerability to Facebook’s security team got the kind of robotic non-response that civilian users often gripe about when reporting problems to the world’s largest social network. So how did he finally get the company's attention? In a dramatic attempt to raise awareness of this privacy hole, he used that very exploit to post a bug report on CEO Mark Zuckerberg's page.
When he hacked the site, Palestinian developer Khalil Shreateh did get Facebook's attention. But he didn't receive the $500 minimum from Facebook's Bug Bounty program, which — in keeping the site's hacker pose — offers rewards to infrastructure sleuths. He didn’t get a thank-you note. Nobody bought him a Coke. Instead, for violating Facebook’s terms of service — "Thou shalt not hack Facebook" — Shreateh got his own Facebook profile bounced from the site, at least temporarily.
When it comes to customer communication, Facebook’s lack of it is legendary. Alerting the media or launching an online petition seems like the only way some disgruntled users could receive resolution. When mastectomy and breast feeding images get knocked off the site, when non-famous people with celebrity names try to prove they're real too, when the most tasteless content remains in plain view, emails to the social network don't work — change only comes when someone draws attention from the outside.
So while hacking Mark Zuckerberg's personal page is no way to "friend" the young billionaire, you can understand why a fed-up security researcher might resort to it.
Hacking Zuckerberg’s wall wasn’t Shreateh’s first course of action. Just like the mom who resorted to a Change.org petition when Facebook banned the photo of her son competing in the Special Olympics or the guy who turned to BuzzFeed after the social network refused to un-memorialize his profile after a prankster reported him dead, Shreateh first attempted the proper channels.
Shreateh, whose first language is Arabic, details his correspondence with Facebook’s security team on his blog. He describes — in shaky but understandable English — the flaw that allows users to post to Facebook timelines of users with whom they aren’t friends. In his report, Shreateh included a screenshot of the bug — a post he was able to make to the profile of Sarah Goodin — Zuck’s college friend and the first woman to join The Facebook (as they called it back in the day).
"I am sorry this is not a bug," is the response he received.
A few frustrated emails later, Shreateh posted to Zuckerberg’s wall.
“First sorry for breaking your privacy and post to your wall,” reads an image Shreateh describes as a screenshot of his post. “I has [sic] no other choice to make after all the reports i sent to Facebook team.”
Within minutes, Shreateh says, he was contacted by Facebook security and asked to detail his exploit. Also, his Facebook account was disabled, he was told, “as a precaution.”
Shreateh's Facebook profile was later reinstated — he's currently using a photo of NSA leaker Edward Snowden — but he shouldn't expect any further recompense. In a contentious forum discussion on Hacker News, which first reported the story, Matt Jones, a member of Facebook's security team, explains that Shreateh violated Facebook's Terms of Service for posting on both Goodin and Zuckerberg's Facebook pages.
When we contacted Facebook, the company stood by Jones' statement. Here's an excerpt:
In order to qualify for a payout, you must make a good-faith effort to avoid privacy violations ... [and] use a test account instead of a real account when investigating bugs. ... [Facebook] will pay out for future reports from [Shreateh] if they’re found and demonstrated within these guidelines.
"Well according to Facebook, 'this is not a bug,'" one Hacker News forum user remarked in the ongoing debate over whether Shreateh deserves the bug bounty. "Which means the feature works as intended. If he is using Facebook as it is intended, then how can he be breaking the [Terms of Service]?"
Do you have a complaint or comment for Facebook? Send 'em a note. Emotionless unresponsive automatons are standing by!
UPDATE: In a (quasi) mea culpa posted on Facebook's security blog Monday evening, the social network's chief security officer Joe Sullivan addressed the hubbub over an unnamed researcher's headline-grabbing bug report, writing in part, "we failed in our communication with him."
In the ensuing caveat, Sullivan notes that this researcher's video explaining the bug, posted on the Internet after the news hit the fan, "is the type of detailed report we encourage."
If only this researcher's bug report to Facebook been thus. Regardless, Facebook will mend it's ways, Sullivan writes:
We will make two changes as a result of this case: (1) We will improve our email messaging to make sure we clearly articulate what we need to validate a bug, and (2) we will update our whitehat page with more information on the best ways to submit a bug report.
Long story, short: Demonstrating a security hole on the Facebook profile of an unsuspecting user remains a Terms of Service violation, and as such, the check is not in the mail.
Helen A.S. Popkin goes blah blah blah about the Internet. Tell her she doesn't know what she's talking about on Twitter and/or Facebook.