It isn't only the president who needs extra security for his BlackBerry. All of us with smartphones that have Internet access, e-mail and the ability to handle sensitive written or financial documents should consider paying closer attention to where and how we're using the devices, experts say.
Most of all, they say, know where your phone is at all times and don't leave it in the care of strangers or by itself on a desk at work. The latter is something a lot of us certainly do.
"There's software out there that will let people image what's on a phone, or download that information in a matter of minutes, put it back on a desk and nobody will know their information is lost," said Michael Kessler, president of Kessler International. The computer and cell phone forensics company works with government agencies, as well as corporate clients and law firms.
"We see that in situations where temporary employees will come into a business, and have access to the work area. People leave their phones on their desks. And it's just a matter of someone picking up the phone, downloading the information from another cubicle, then sticking the phone back on the desk, and you never know your information has been downloaded."
Johannes Ullrich, chief research officer for the SANS Institute, a security research organization, says the biggest threat for cell phone users is leaving their devices behind somewhere, or losing them. And perhaps putting too much data on the device.
"The information stored on a phone should be limited to information that is required while on the move," he said. "Some phones allow the user to store spreadsheets and other office documents. If any passwords are stored on the phone, they should be encrypted."
Check the cab
In a report last fall, "Guidelines on Cell Phone and PDA Security," the National Institute of Standards and Technology's Computer Security Division cited a report which said there would be 8 million phones lost in 2007, including 700,000 smartphones.
The government agency also said that one Chicago taxi company recorded more than 85,600 cell phones and 21,400 personal digital assistants left behind in the company's taxis during a six-month period, compared to more than 4,400 laptops.
So far, NIST noted, problems from malicious software, or malware, including spyware, viruses and spam, have been "limited" on cell phones compared with desktop and networked computers.
The agency said that's largely because of the number of different operating systems, including Windows, BlackBerry, Apple's Mac OS, Linux, Symbian and Palm, on cell phones which helps fragment the number of "potential homogeneous targets."
That also means there is no "one size fits all" security solution for cell phones, but there are some common issues to monitor.
Wi-Fi can be more vulnerable
As smartphones grow in popularity, so too does interest by thieves, not necessarily for the devices but for the information they hold.
That information can be easier to obtain, for example, if you're getting to the Internet using Wi-Fi from your cell phone, versus a wireless carrier's network.
While Wi-Fi generally transmits data more quickly than 3G, or a third-generation wireless network, it's also more vulnerable unless you take extra steps to encrypt what you do when using the phone.
"Wi-Fi is dramatically less secure than a cell phone network," said Dan Hoffman, chief technology officer of SMobile Systems, which makes cell phone security software, a growing industry.
"If you're on a 3G network, there will be encryption by the wireless carrier. When you're on Wi-Fi, there's not going to be encryption, and your data will literally be flying through the air."
"The phone network is reasonably secure," said Ullrich. "However Bluetooth and Wi-Fi have a number of problems that allow others in the proximity to listen in."
Mobile banking Web sites do take extra security measures to protect users' data. But other sites do not, leaving it up to the user to do so.
"There are ways to encrypt data using Wi-Fi, but it's more an issue of the user being aware" of knowing do to that in the first place, Hoffman said.
Bluetooth awareness
Bluetooth, the short-range wireless technology used in cell phone headsets, can also provide an entry point for an intruder or eavesdropper.
"Depending upon how it is configured, Bluetooth technology can be fairly secure," the federal Computer Emergency Readiness Team noted in a "Cyber Security Tip" sheet last summer.
However, CERT said, "unfortunately, many Bluetooth devices rely on short numeric PIN numbers" — the default, out-of-the-box setting for many headsets is "0000" — instead of more challenging passwords or passphrases. Again, it's up to the user to change the default password.
Without doing so, someone who's within about 30 feet of your headset could access or corrupt your data.
"One example of this type of activity is called 'bluesnarfing,' which refers to attackers using a Bluetooth connection to steal information off of your Bluetooth device," CERT said.
"Bluetooth has been used in the past to trick users to install viruses or to download phone books from the phone," said Ullrich.
Put Bluetooth in 'hidden' mode
CERT recommends disabling Bluetooth devices when they're not being used, and when they are, put Bluetooth in "hidden" mode, which prevents other Bluetooth devices from recognizing your device.
It's also important to be aware of where you're using Bluetooth to "pair" a phone and headset, or put the two in what's known as "discoverable" mode, so that the devices can find each other. Being in a public wireless area, or "hot spot," poses a greater risk for interception, CERT said, than if you're at home or in your car.
One of the first things smartphone users should do is establish a password for access to the phone itself. Most of us don't really want to do that — it delays us from quickly getting to our e-mail or the Web, but it is a basic, preventative measure.
Once your data is on your smartphone, back up that information to a computer, and make sure you do such backups regularly.
Hoffman of SMobile Systems says even stronger steps are needed.
"What people need to be able to do is to remotely lock their devices, be able to remotely back up the data and be able to remotely delete the data so nobody can access their devices."
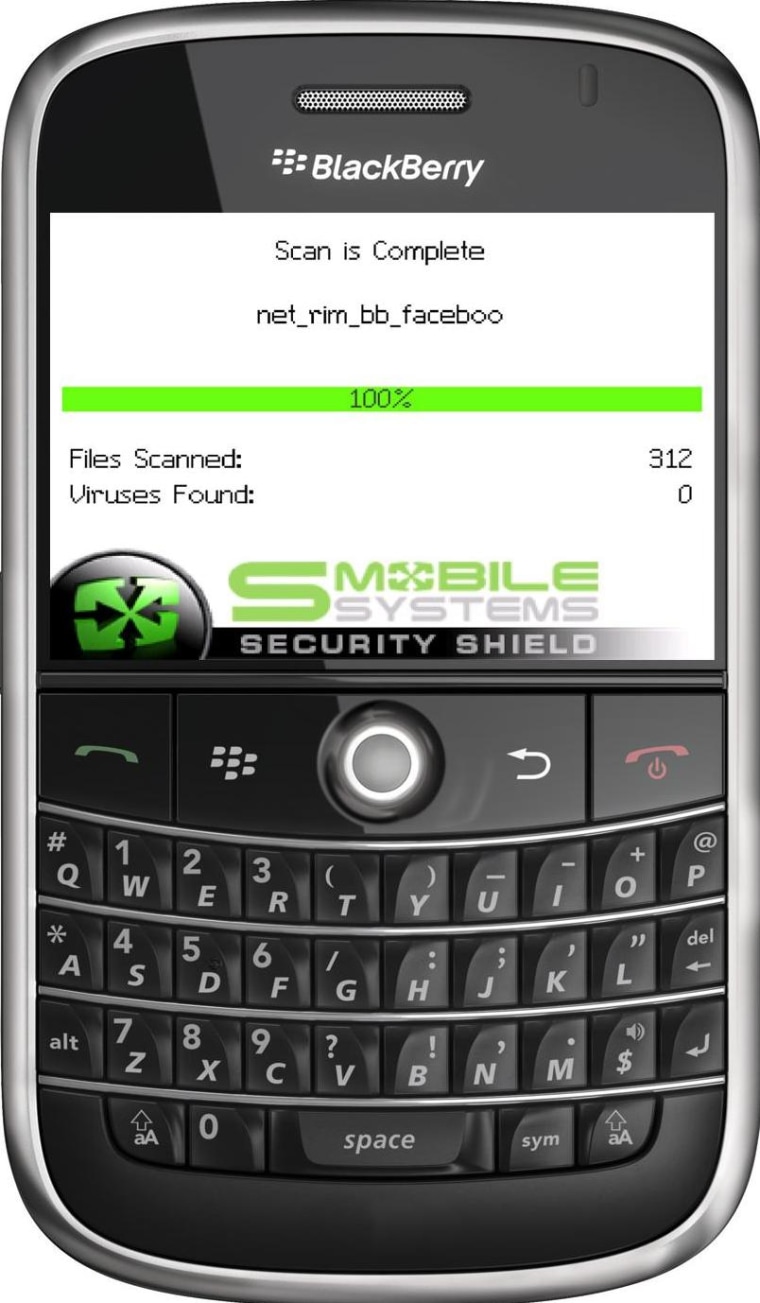
His company's Secure Shield software for consumer mobile phones does that, and also provides anti-virus, anti-spam and firewall protection. A version for BlackBerrys costs $39.99, and is $29.99 for Android, Windows Mobile and Symbian phones. The company also has software in the works for the iPhone.
Like computer anti-virus software, the phone security software must be renewed every year.
McAfee, one of the leading makers of security software, said Monday in an annual report about mobile security that half of all global phone manufacturers reported malware infections, voice and spam attacks, third-party application problems or "incidents" that caused problems with wireless carriers' network capacity.
"Overall, there has been a dramatic upswing in the number of incidents ... including exploits that affected manufacturers' device functionality, users' privacy and even network or service capacity — in many cases by more than double over the last year," the company said.
Corporate 'wipes'
A "remote wipe" feature, to delete information from the device if it has been lost or stolen, is available to BlackBerry customers whose companies use BlackBerry Enterprise Server
Remote wipe capabilities are also offered on other devices, including the iPhone and phones using Windows Mobile, when they use Microsoft's Exchange Server. As with BlackBerrys, an IT administrator must give the OK for a remote wipe to be done.
BlackBerrys, made by Research In Motion, come with several strong security options for business and non-business users, including encryption. It's up to the user to enable, or turn that encryption on.
Also, e-mail messages sent and received through the BlackBerry Internet Service are protected using Secure Sockets Layer protocol, a RIM spokesperson said, "if the external messaging server supports SSL encryption." Content protection, too, can be enabled to protect information such as address book, calendar and memo entries.
Even so, President Barack Obama's wanting to keep his BlackBerry raised concerns. It was decided that he will continue to use the device, but on a very limited basis with a limited number of people.
A long-distance eye
Another company, Maverick Mobile Solution, is testing a program for Symbian-based phones (those largely from Nokia) that not only encrypts data, but also sends a text message to the owner with the location of the stolen phone.
"The more information and the more functions a phone can do, the more susceptible it is to someone getting that information, either through loss or through a spyware-type of software," said Kessler of the forensics firm.
"The most important thing is not to lose it — because once you lose it, all that data is susceptible."